Plesk offers the possibility to configure the Web Application Firewall (plesk modsecurity) in the administration menu.
What is modsecurity?
Plesk Modsecurity is a Web Application Firewalla firewall that allows access to web applications like content management systems (wordpress, joomla, etc.), or other applications and prevents known attacks.
The advantage of modsecurity is the possibility to analyse accesses first and to define accordingly which accesses are legitimate and which have to be rejected directly.
Of course, it is impossible to set up everything yourself, but there are providers who offer ready-made rules, some of them live, and can thus react directly to current threats.
For example, if a new attack on a particular content management system occurs, these providers update their rules and modsecurity can then block these accesses before an infection occurs.
For Plesk users, this is a good program to prevent most known attacks on your application.
In connection with a firewall which filters and blocks the IP addresses you can secure your server well.
External solutions
An external firewall such as Cloudflare WAF works similar with partly the same rules, but offers the possibility to fend off attacks before they reach the server. An optimal protection would therefore be a Web Application Firewall from Cloudflare or Imperva/Incapsula and then only use special rules on the server. This saves computing power and thus speeds up the page considerably.
Alternatively, modsecurity can of course be set up as a reverse proxy and thus use all other web servers besides Apache.
How to install Plesk modsecurity?
As administrator, simply click on Settings and select the Web Application Firewall (modsecurity) there.
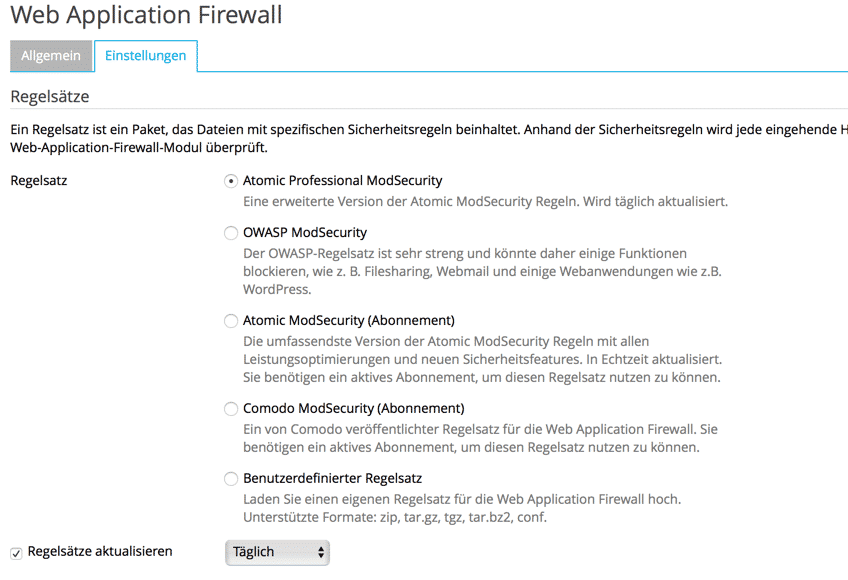
There are here still the inexpensive comodo rules offer a good protection against all threats. However, the license must always be updated.
So if you're too lazy, you can simply use the Atomic subscription rules which provide live protection. But you have to keep in mind that this is not quite true, because the web server has to be reloaded and then the 502 Bad Gateway problem occurs again.
Practical is the Atomic Professional protection which is available together with Cloudflare in the package. Here you can easily remove the web application firewall from Plesk and switch your domains to Cloudfalre as an additional protection mechanism.
The problem here, however, is that you can only protect subdomains, so your site should only be accessible at www.ihrefirma.de and not at yourcompany.com. Alternatively one can use as Cloudflare partners also the Cloudflare Nameservers and offer thus a complete protection.
Because the license prices of Plesk and the add-ons are constantly being increased incalculably, a provider should perhaps consider external licensing.
There are interesting solutions directly from atomicorp, or another way to activate mod_security on the server, or to use directly an external protection like cloudflare.
A good replacement for Plesk because of the uncertain privacy issues with all the plugins would be a German manufacturer of the popular admin panel "Liveconfig".
Plesk extensions with ModSecurity support
There are some extensions for Plesk with which you can secure the server. These also include modsecurity rules to defend against known attack patterns.
Imunify360
In addition to its own operating system, Cloudlinux also offers the security solution Imunify360. This offers a very wide range of functions for all security areas of the server. The firewall monitors the logs and, if necessary, blocks IP addresses that, for example, connect too often with false login data that are on a block list, or want to access with known attack patterns. You can also simply activate a DoS protection and scan all files for known malware and also partially clean them. In addition, there is also a so-called KernelCare function that automatically updates the Linux kernel without the need to reboot the system. The extension can be obtained directly from Cloudlinux and costs more than Plesk itself.



