With Plesk you can activate a simple and free protection against attacks.
In the Plesk settings, you can configure the Fail2ban service when logged in as administrator.
The fail2ban service
fail2ban monitors the log files of the activated services and searches for defined patterns and IP addresses. The program is supposed to secure against Denial of Service attacks by marking numerous accesses from always the same IP address to the same service and then by the Firewall can be blocked.
This usually works quite well against automated tests for passwords of the SSH service. However, with many configuration files the system is no longer suitable.
You can define many settings like the exact pattern after the program should report alarm, or the time the attacker's IP address should be blocked.
The requirements of the individual services are then defined in so-called jails.
The Jails
Generally nothing is activated for the time being. A reasonable protection would be the SSH access and possibly the FTP access, whereas it makes more sense to change the standard SSH port from port 22 to another port.
Another good protection would be access to WordPress xmlrpc.php or wp-admin and joomlas /administrator/index.php . Here there are also from time to time DoS attacks which can then be blocked relatively quickly.
However, fail2ban also slows down the system noticeably when the server is accessed frequently. Meanwhile there are quite good alternatives like csf as a firewall solution with LFD or in this context also the finished package imunify360.
This offers the attacker the possibility to unlock the system again, e.g. when DoS attacks occur. This may be absurd at first glance, but most attacks are fully automated by bots. However, it happens from time to time that regular accesses are also marked as attacks. In this case, however, the person can then unlock again by entering a password.
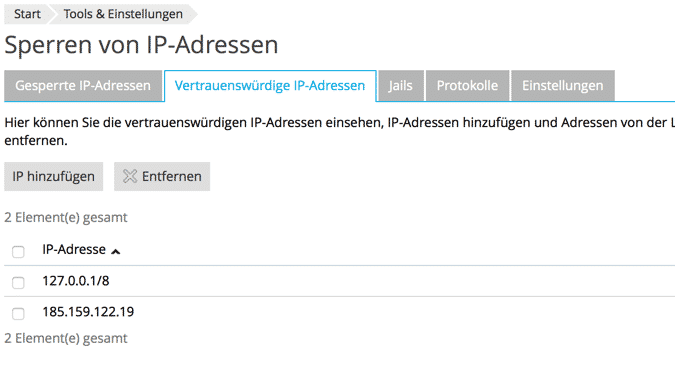
Whitelist and Blacklist
Of course you can also put single IP addresses and ranges on the white or black list.
For all those who find the Plesk license far too expensive, fail2ban offers at least a basic standard protection that costs nothing and can be managed via the interface.